What Is a Ransomware Attack?
Updated on October 10, 2022, by Xcitium

Ransomware Attack Explained
In recent years, businesses, health facilities and even government agencies have suffered a form of malware attack that cripples their day-to-day operations for some time. Unlike some malware attacks that damage and steal data, this particular attack locks you out of your computer and sensitive data until you’re able to pay a ransom before you can recover your system.
What’s a ransomware attack? You do guess that right. The above illustration points to ransomware mode of attack. We’re going to dig deep into what’s a ransomware attack is, how it affects computers, preventive measures, and what to do when this dreadful con malware attacks you. But first;
What Is Ransomware?
Ransomware is a type of malware that encrypts data in your computer and locks you out. This malware doesn’t destroy your data but limits your access and request for a ransom before the victim can regain access. This is usually aided by an individual who has developed the malware to get money from people fraudulently.
Most victims of ransomware are made to pay a huge sum before they are allowed to recover their systems. The manner of attack makes it difficult to crack the codes as the malware immediately encrypts your data which can only be decrypted with a unique key from the ransomware criminal.
How Do You Know Of A Ransomware Attack?
This malware doesn’t slow down your computer or cause any bug, so it’s difficult to spot it before it unleashes its mayhem. Most victims of ransomware realized that they were under a ransomware attack after receiving the on-screen notification requesting for a ransom.
If by any means you’re able to detect the presence of the malware on your computer, you do get rid of it before it encrypts your data.
Why Is It Difficult To Trace The Payment Sent To Ransomware Criminals?
If you know a thing about cryptocurrencies, you will understand that this form of digital payment leaves no traces. It’s a form of digital payment without any third-party regulations. And this is the preferred payment method for ransomware assailants. Virtually all ransomware attackers have requested for the ransom to be paid in Bitcoin. This has made it difficult to fish out the perpetrators of ransomware attacks.
How Does Ransomware Enter A Computer?
Phishing has been the entryway for several ransomware attacks. Before anyone becomes a victim of a ransomware attack, odds are you might have downloaded an application containing the malicious code or clicked an attachment sent to your email. With any of these, the malware enters your computer to carry out its assignment.
Phishing is spread through emails, calls and messages on social media platforms. The attackers are always deceptive in their means of operations. They do send emails that mimic your bank, ISP, healthcare provider, etc. If you don’t check carefully to detect the difference, you may click the attachment thinking it’s from your service providers. You should verify any email sent to you before taking any action like opening an attachment.
Another way you can get infected is through pop-ups on websites. Be sure you don’t click on any random website asking you to update your outdated software. Most of them are scams.
What To Do When Attacked By Ransomware?
A ransomware attack is not a pleasant experience. The attackers do target your most important data. If you know your computer under attack houses essential data that are not backed up, you want to play along with the criminal’s requirements. But if you have no too much sensitive information and you have them backed up, you may want to wipe off all data on your computer completely. However, the best thing is to avoid being a victim of ransomware.
Preventing Ransomware
Basic cybersecurity rules can help you prevent ransomware attacks. This include:
- Avoid opening suspicious attachments
- Backing up your data
- Keep all your applications and operating system up-to-date
- Set a strong password and do not use one password for all your accounts
- Avoid the use of public Wi-Fi
- Get a strong antivirus
- Use advance endpoint protection.
Final Thoughts
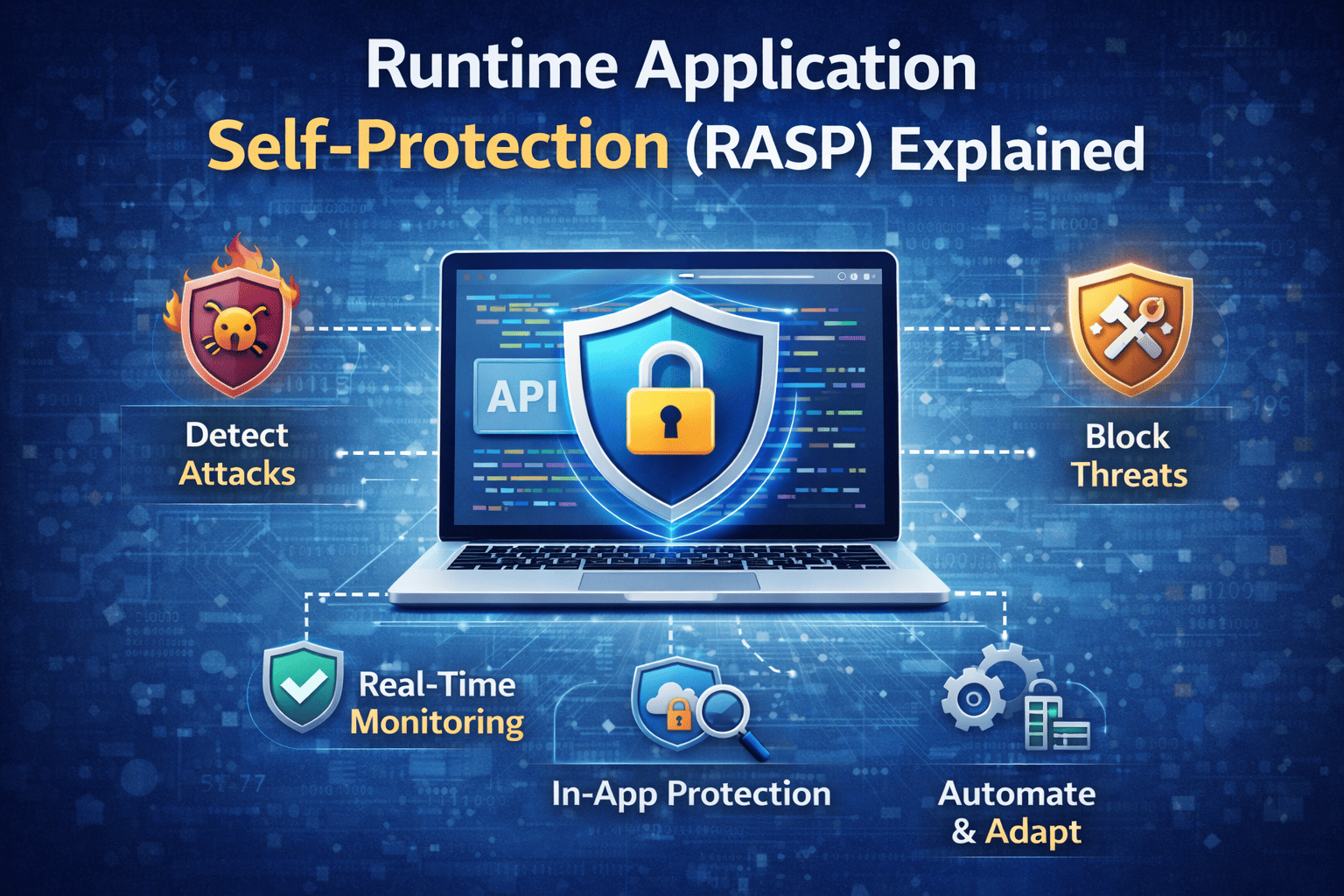
You may wonder if all the victims of ransomware attacks did not adhere to cybersecurity best practices. Perhaps they did, but ransomware malware is quite deceptive, it tricks antiviruses and firewalls to think it’s not harmful. This is why businesses are now deploying advance endpoint protection to block advanced malware like ransomware. This security system uses advanced technologies like IoT, AI, etc., to detect and stop sophisticated malware.
Curious to learn more about advanced endpoint protection? Go here for details.