
- December 01, 2025
- 6 mins
If you’re searching for what does ransom mean, you may already know it typically involves a...
- December 01, 2025
- 7 mins
If you’re searching for what peripheral devices, you’re likely trying to understand the...

- December 01, 2025
- 6 mins
If you’re searching for what is the OSI model, you’re probably trying to understand one of...
- November 28, 2025
- 6 mins
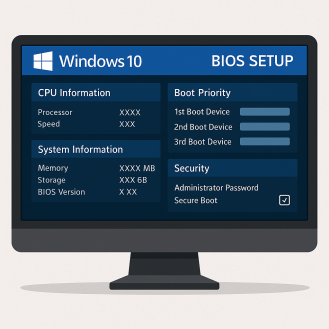
If you’re trying to figure out how to boot into BIOS Windows 10, you’re in the right place....

- November 28, 2025
- 6 mins
If you’re searching for how to block incognito mode, you’re not alone. Whether you’re...

- November 28, 2025
- 7 mins
Is your smartphone behaving strangely lately? Maybe it’s heating up for no reason, your...

- November 27, 2025
- 6 mins
In today’s hyper-connected world, mobile phone security applications are no longer...

- November 27, 2025
- 5 mins
Mobile devices are now the backbone of modern business operations. From smartphones and tablets to...

- November 27, 2025
- 6 mins
Cyberattacks are more aggressive, more sophisticated, and more frequent than ever before. From...







